Overview
A critical Server-Side Request Forgery (SSRF) vulnerability in GitLab has recently gained renewed attention after being confirmed as actively exploited in the wild.
Table of Contents
Although the vulnerability was originally disclosed and patched in 2021, many self-hosted GitLab Community Edition (CE) and Enterprise Edition (EE) instances remain unpatched, making them attractive targets for attackers.
This flaw allows unauthenticated attackers to abuse GitLab as an internal proxy, potentially exposing internal services, cloud metadata, and sensitive infrastructure components.
Overview
A critical Server-Side Request Forgery (SSRF) vulnerability in GitLab has recently gained renewed attention after being confirmed as actively exploited in the wild.
Although the vulnerability was originally disclosed and patched in 2021, many self-hosted GitLab Community Edition (CE) and Enterprise Edition (EE) instances remain unpatched, making them attractive targets for attackers.
This flaw allows unauthenticated attackers to abuse GitLab as an internal proxy, potentially exposing internal services, cloud metadata, and sensitive infrastructure components.
What Is SSRF and Why Is It Dangerous?
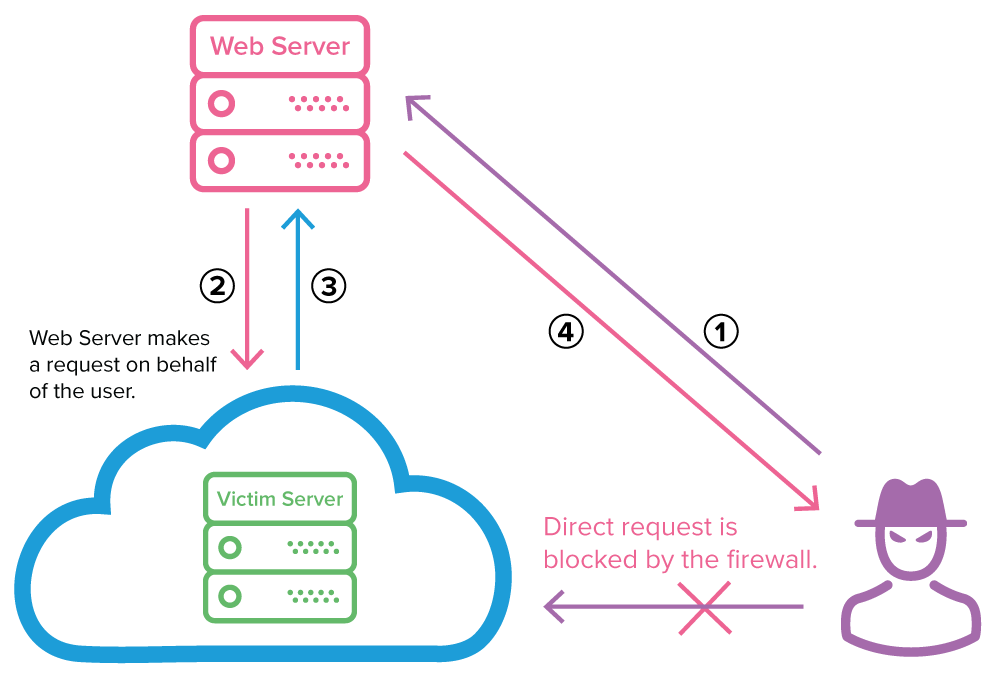
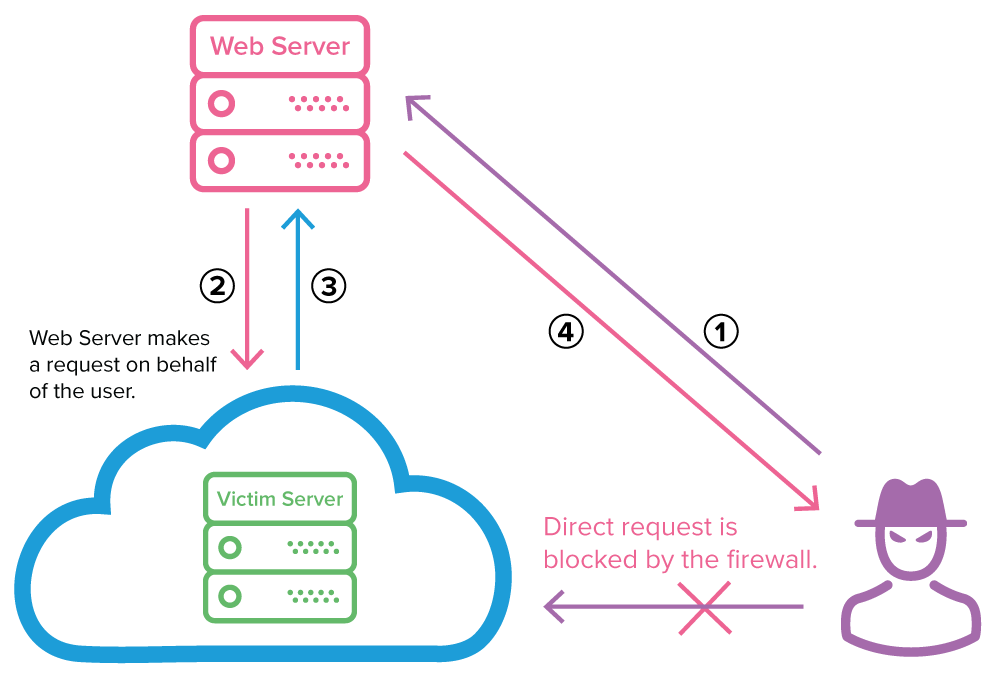
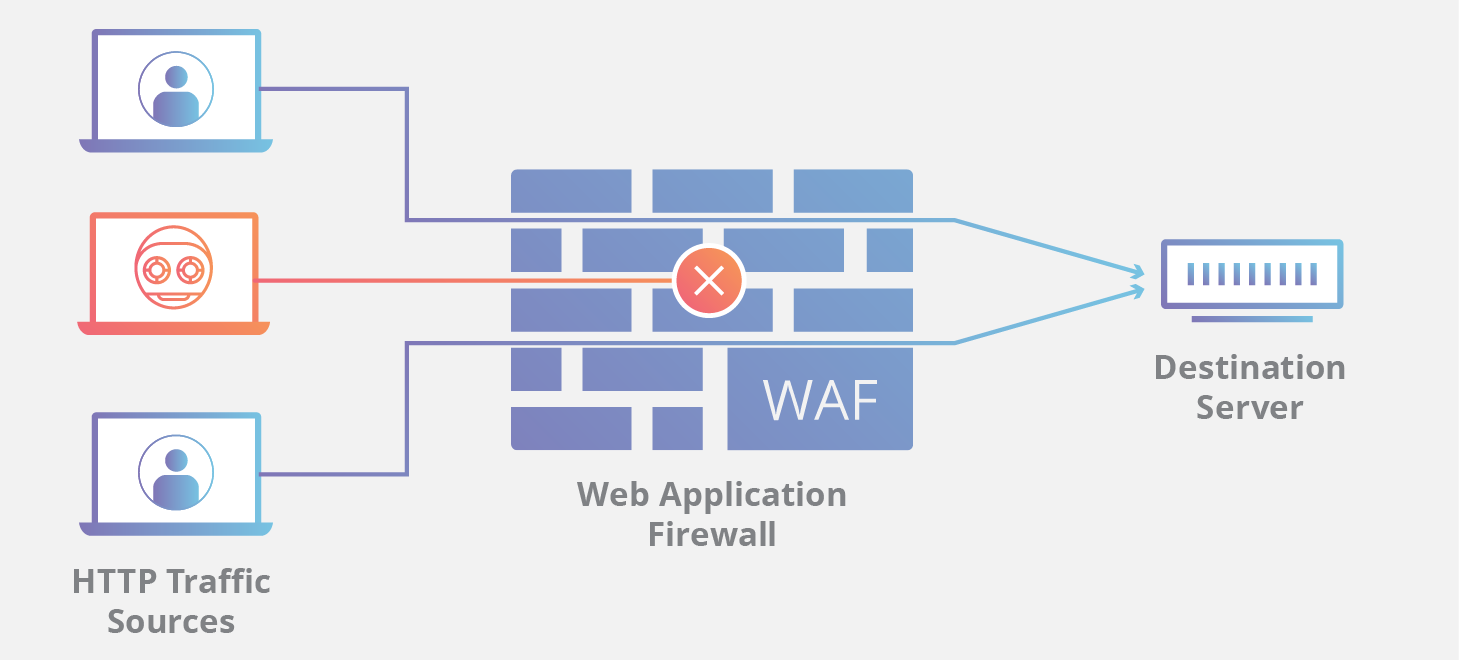
Server-Side Request Forgery (SSRF) occurs when an application fetches a remote resource based on user recallable input without proper validation.
In a DevOps platform like GitLab, SSRF can be extremely dangerous because it allows attackers to:
- Access internal network services behind firewalls
- Query cloud provider metadata endpoints
- Exfiltrate credentials, tokens, or secrets
- Perform internal network reconnaissance
- Chain SSRF into privilege escalation or RCE
Because GitLab often has broad network access, SSRF turns it into a powerful pivot point inside enterprise environments.
Technical Details: CVE-2021-39935
Vulnerability Summary
- CVE ID: CVE-2021-39935
- Affected Component: CI Lint API
- Attack Vector: Remote, unauthenticated
- Impact: Internal network access, data exposure
- Status: Actively exploited
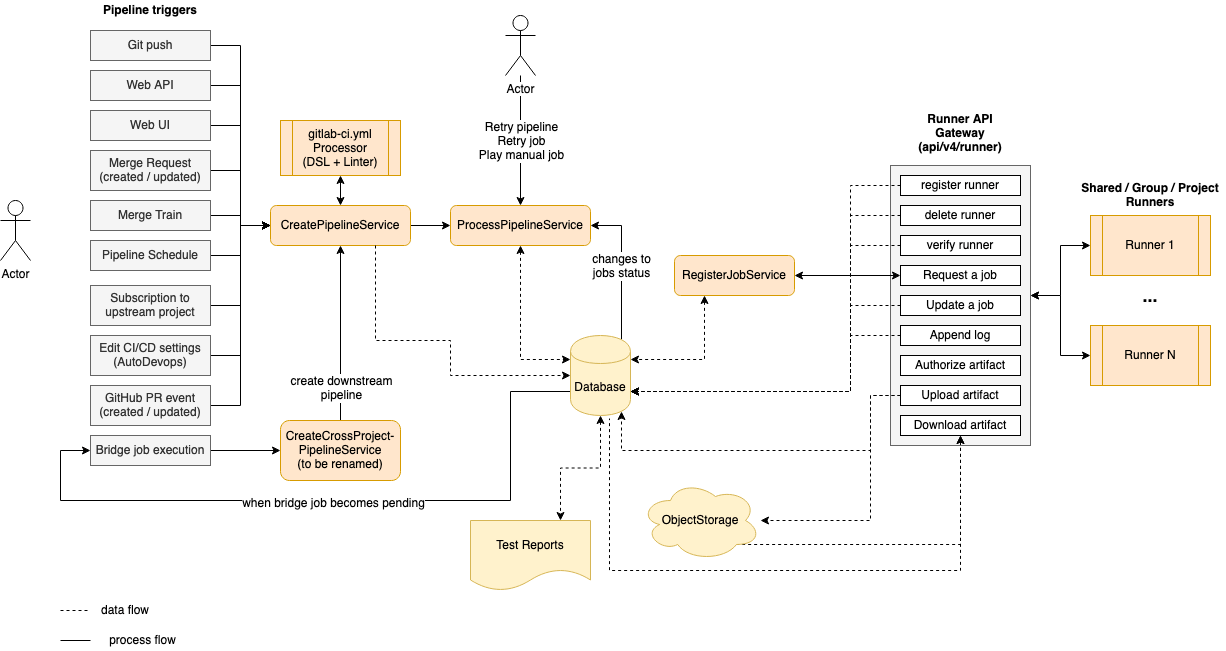
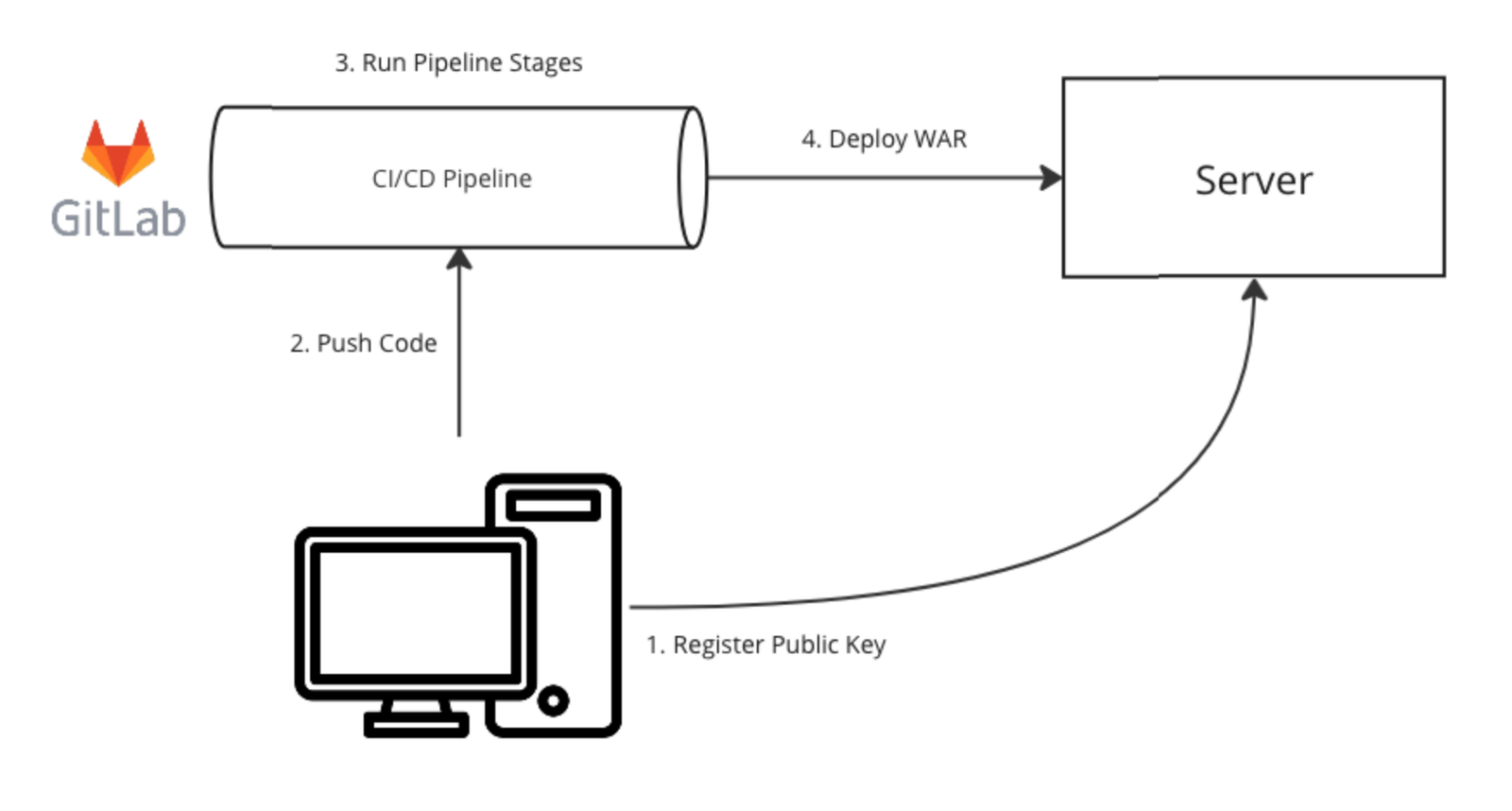
The vulnerability exists in the CI Lint API, an endpoint designed to validate .gitlab-ci.yml configurations.
Due to insufficient validation of supplied URLs, an attacker can craft malicious requests that force the GitLab server to issue arbitrary outbound HTTP requests.
Why This Is Critical
- No authentication required
- Works on exposed GitLab instances
- Enables internal service enumeration
- Can access cloud metadata services (AWS, GCP, Azure)
Security agencies have now added this CVE to known exploited vulnerability catalogs, confirming real-world abuse.
Who Is Affected?
You are affected if you run:
- Self-hosted GitLab CE or EE
- Internet-accessible GitLab servers
- Older GitLab versions not patched since 2021
✅ Not affected:
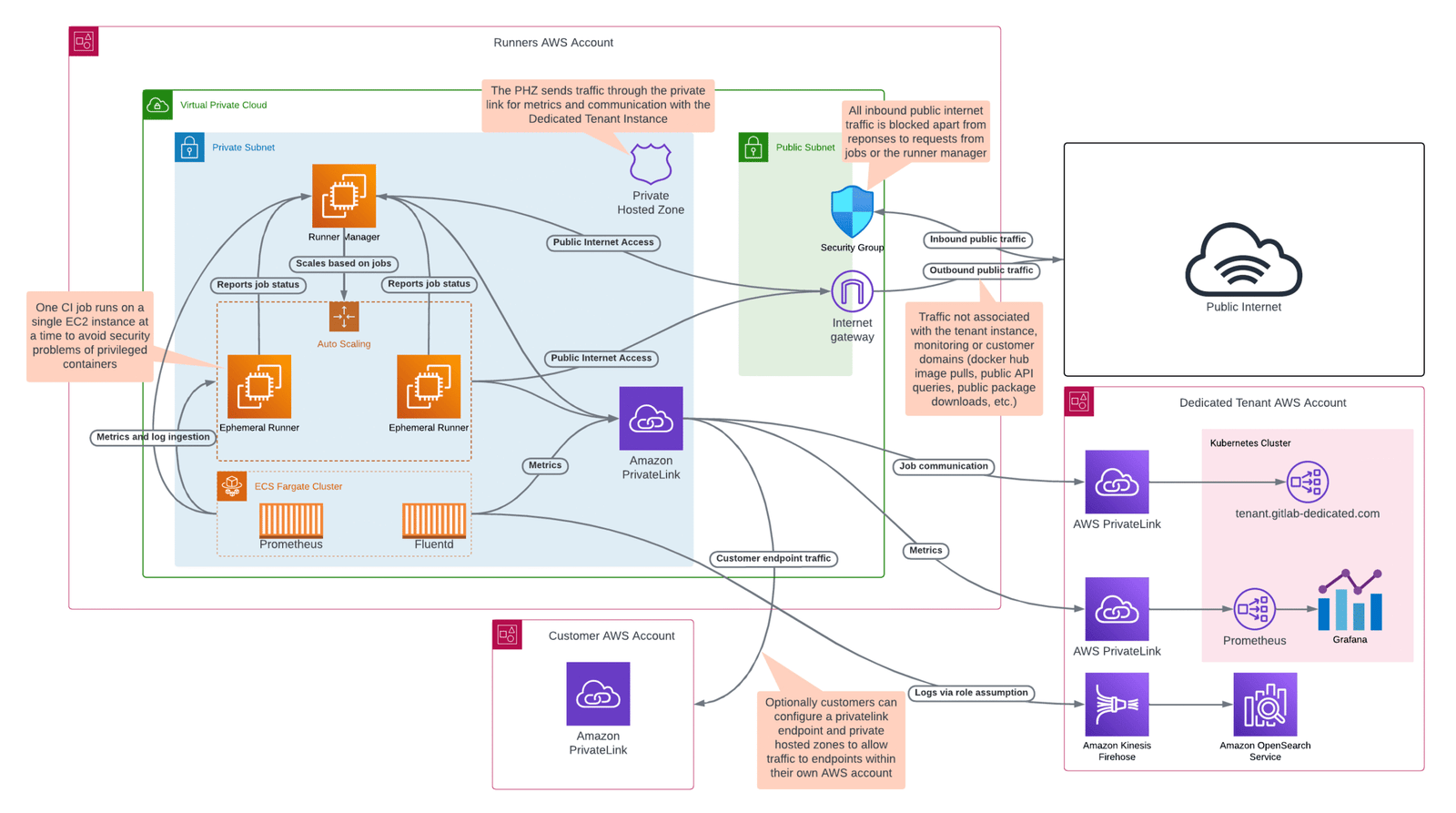
- GitLab.com (SaaS)
- GitLab Dedicated (managed service)
GitLab’s hosted platforms were patched early, but on-premise and cloud self-managed installations remain at risk.
Real-World Impact of Exploitation
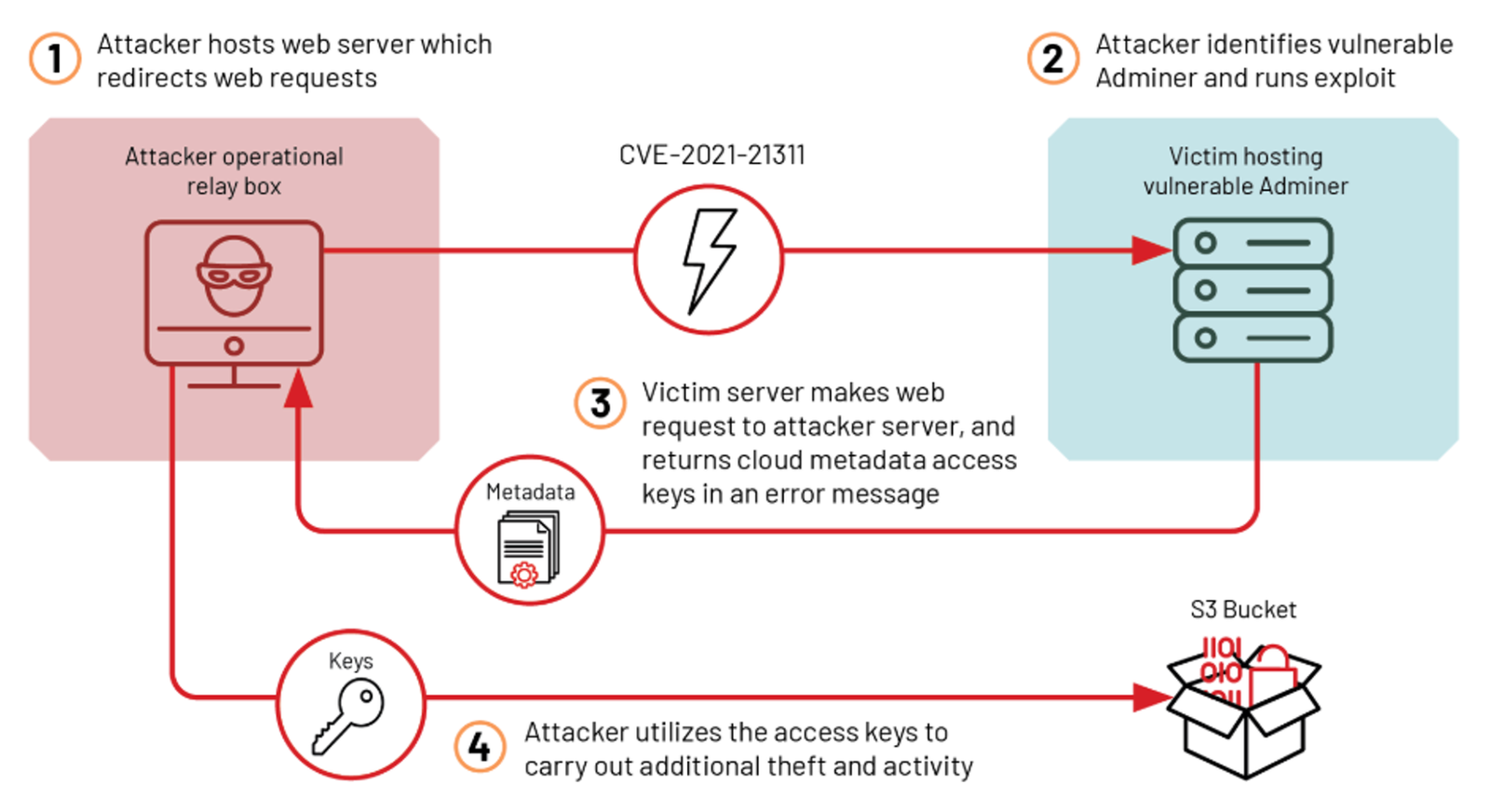
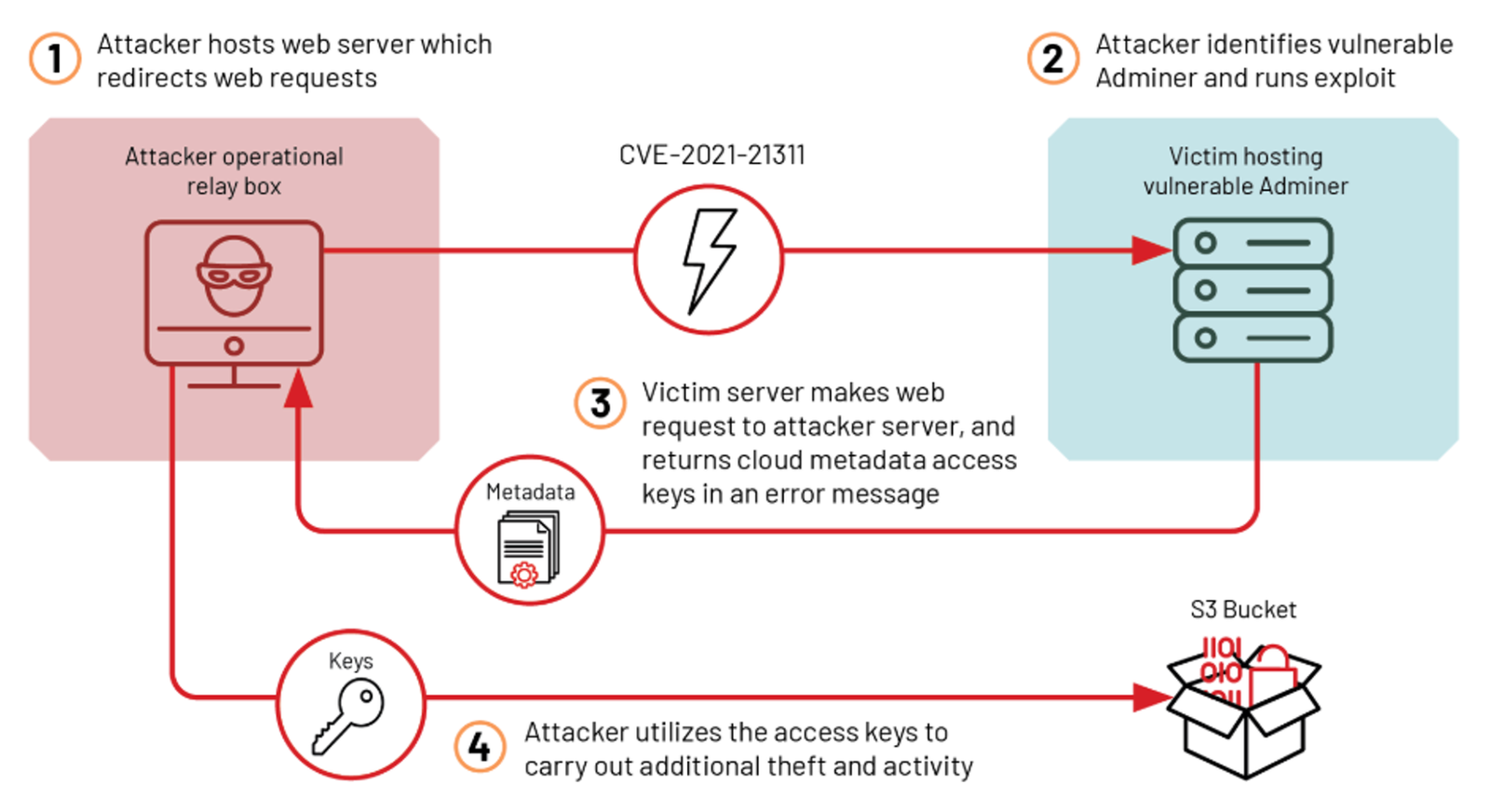
An exploited SSRF vulnerability in GitLab can lead to:
🔥 Infrastructure Compromise
- Internal service access (databases, admin panels)
- Lateral movement inside private networks
- Metadata credential theft
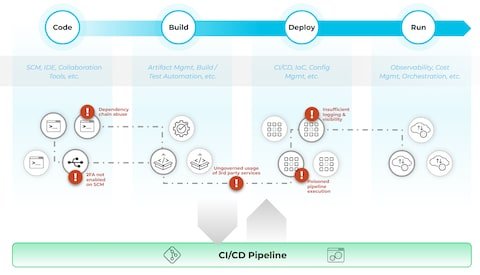
🔥 CI/CD Pipeline Exposure
- Leakage of CI variables and secrets
- Access to build artifacts and deployment configs
- Potential supply-chain attacks
🔥 Cloud Account Takeover
- Harvesting IAM credentials
- Abuse of cloud APIs
- Persistent compromise of cloud environments
Mitigation & Security Recommendations
1. Patch Immediately
Upgrade GitLab to the latest supported version that includes SSRF fixes.
2. Restrict Outbound Network Access
- Apply egress firewall rules
- Block access to internal IP ranges and metadata endpoints
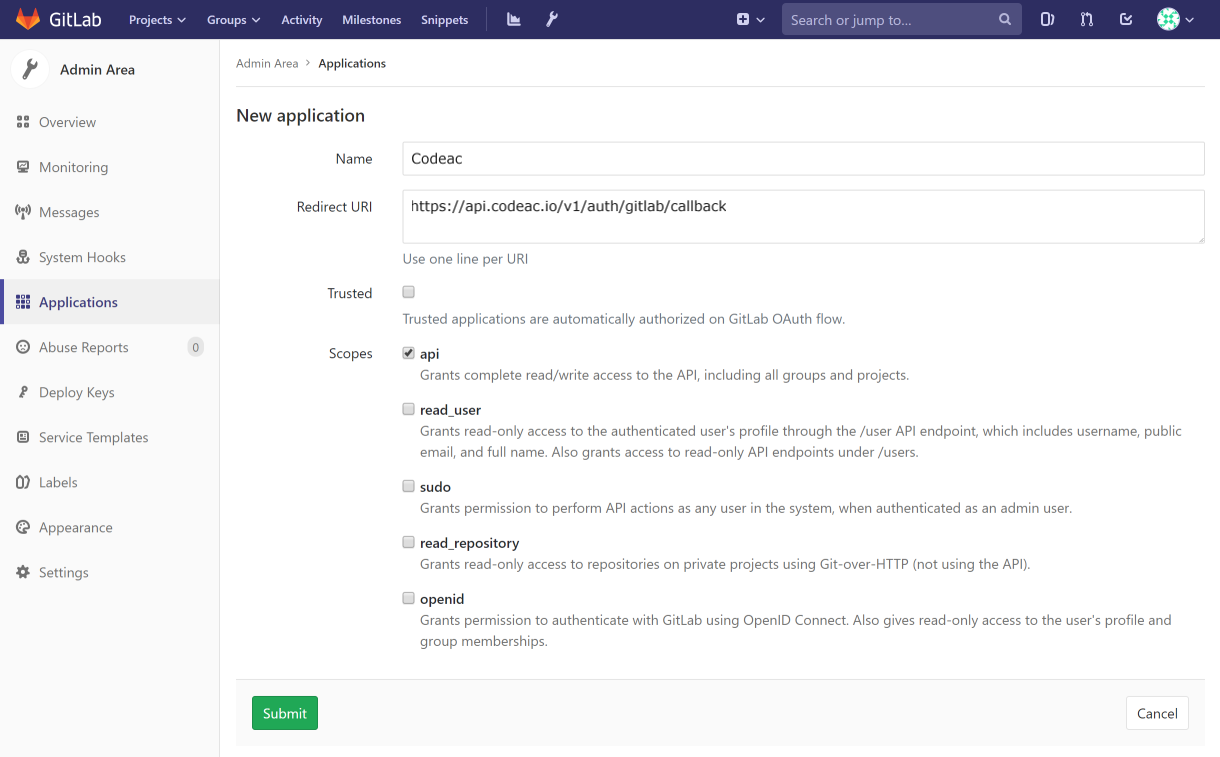
3. Limit API Exposure
- Restrict access to CI Lint API
- Avoid exposing GitLab admin APIs publicly
4. Monitor & Detect
- Log outbound HTTP requests
- Detect unusual internal IP access
- Monitor CI/CD configuration changes
5. Harden GitLab Configuration
- Apply least-privilege principles
- Restrict webhook and integration usage
- Review proxy and dependency settings
SEO FAQ (Rich Snippet Friendly)
Is the GitLab SSRF vulnerability still exploitable?
Yes. CVE-2021-39935 is confirmed to be actively exploited on unpatched self-hosted GitLab instances.
Does GitLab.com have this issue?
No. GitLab.com and GitLab Dedicated are already patched and not affected.
What is the risk level?
High to Critical, depending on network exposure and cloud integration.
Final Thoughts
The GitLab SSRF vulnerability highlights a recurring problem in DevOps security:
unpatched infrastructure + over-trusted internal services = high-impact breaches.
If you run GitLab in your own environment, patching alone is not enough. Network-level controls, monitoring, and API hardening are essential to prevent SSRF from turning into a full infrastructure compromise.